This chapter describes how to configure Ubiquiti with USG, with a version equal to or greater than 5.12.66.
Before proceeding further with the configuration, you need to configure Wi5stars with a domain and a gateway as described in Adding a New Gateway.
The prerequisites required for configuration are:
When you set the Secret Radius in your %DEVICE” do not exceed 12 digits code and do not use symbols, otherwise UniFi will not send it correctly.
Now inside Wi5stars, select your Gateway, click the dropdown menu, choose Edit.
Expand the General Data session.
In the Hardware Type field, choose Ubiquiti.
Login to your Unifi controller and click the Settings icon on the bottom left.
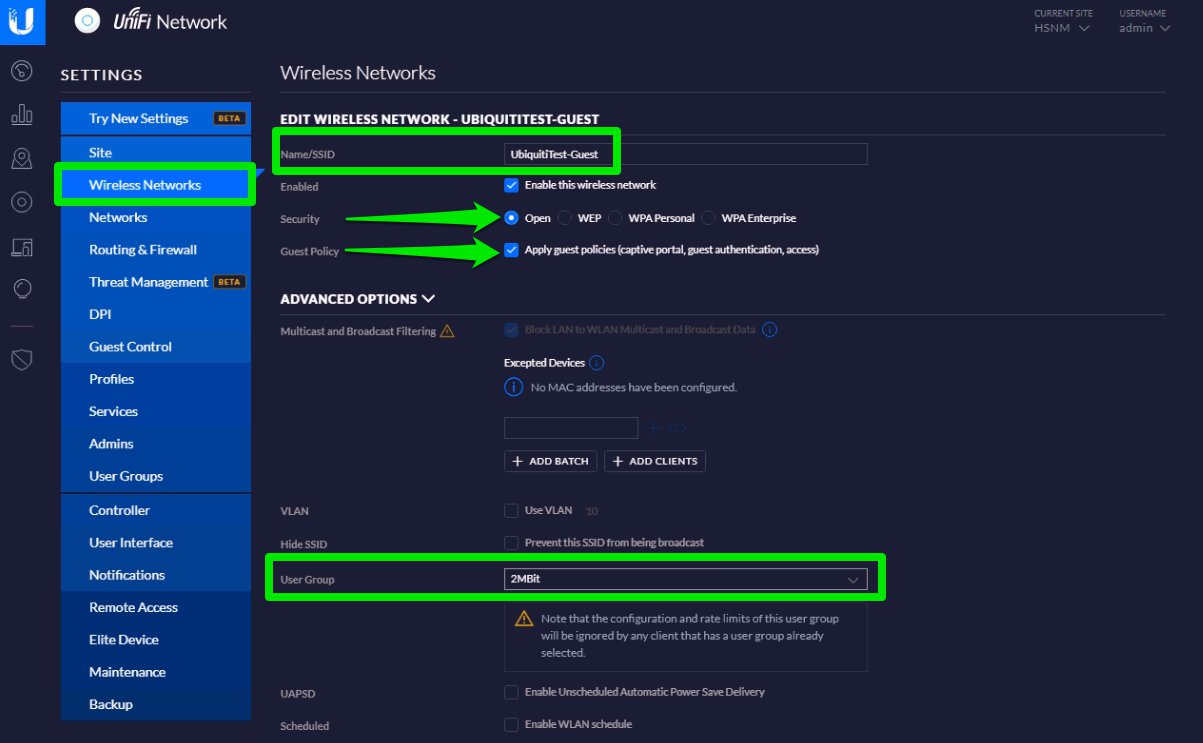
On the left menu, scroll down to Wireless Networks and click Create New Wireless Network.
Configure with:
Optional: expand the Advanced Options session and select the User Group (traffic shaping) that you will configure in the “User Group (Option)” paragraph.
Once completed, click the Save button to save the entry.
On the left menu, select Profiles and create the Radius profile.
In the Radius Profile header, enter the details as follows:
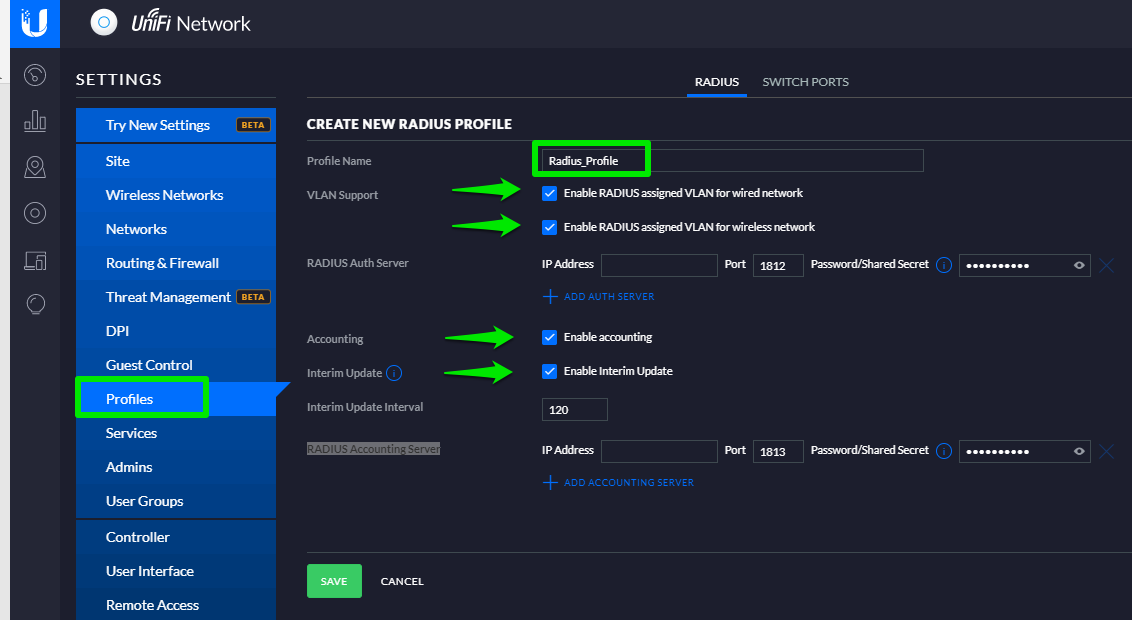
In the IP Address fields enter the public IPs of the Radius server of your Wi5stars Radius and its relevant Secret.
In order to add the Secret you need to get it from your Wi5stars as described in the Radius Secret paragraph.
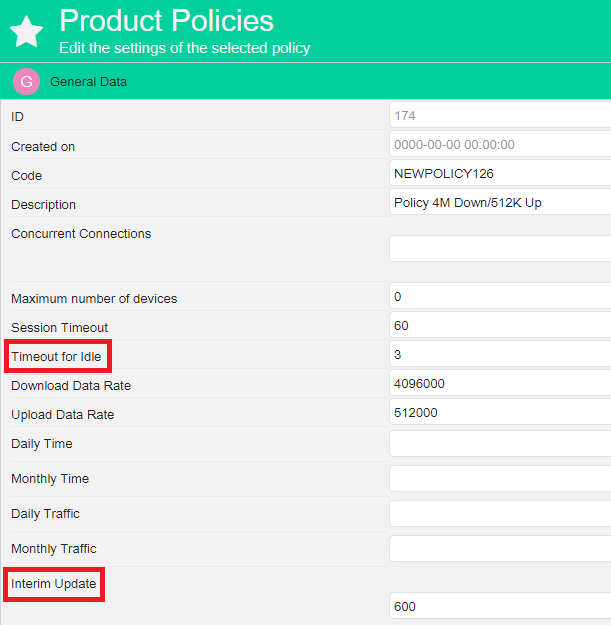
Troubleshoot: Interim Update
It will use the value you edit here and not the value you enter in the Product Policy. This value must be equal to or lower than the value entered in the products you set up for the users.
Ubiquiti UniFi Controller does not support or has errors in accounting radius. The data is correct only if the system is able to reach the UniFi controller (normally with NAT or VPN rules) and compensate directly for failings. If not possible, we recommend you to use this type of gateway only to authenticate users. You cannot parametize the user data rate in the Products, you can define it only in the controller.
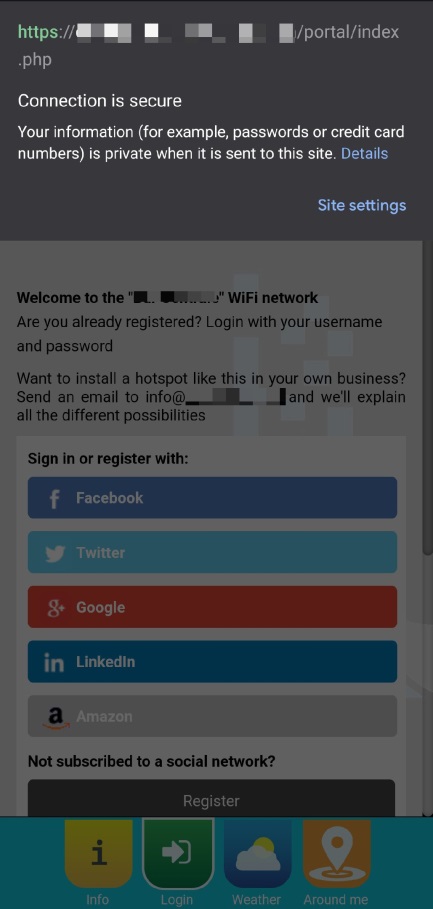
Now, you need to set up the guest policies. From the Settings menu on the left, open the Guest Control page.
In the Guest Policies header, enter the details as follows:
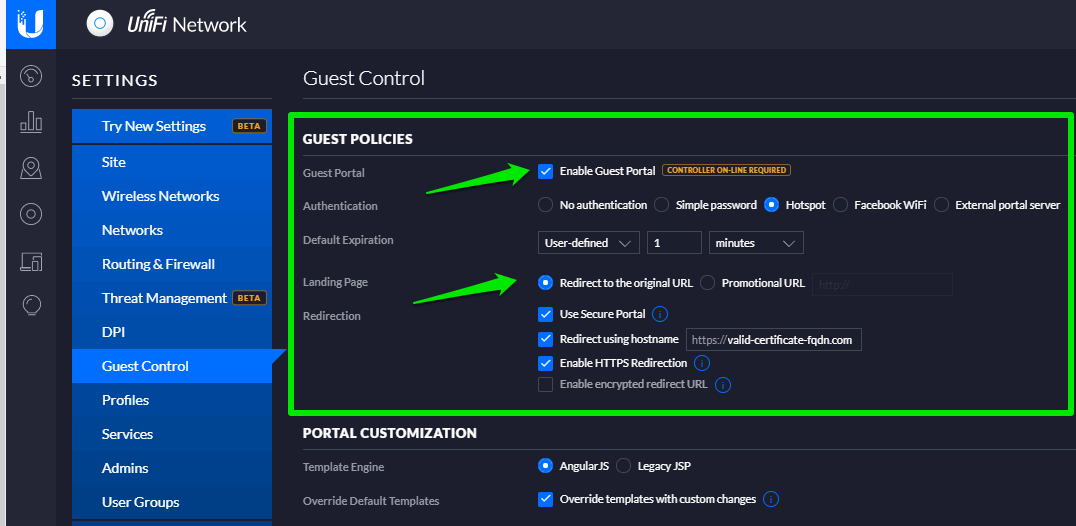
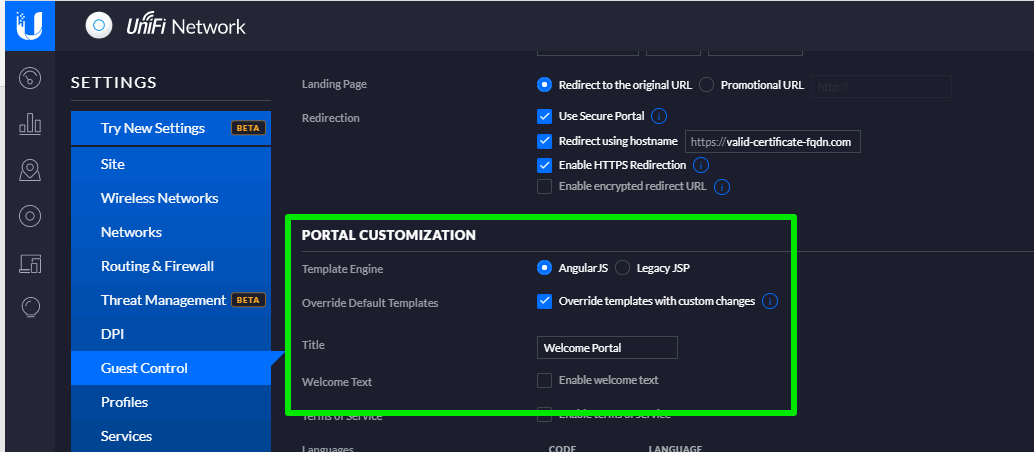
Once you have completed the above steps, in the Portal Customisation header, enter the details as follows:
Ignore any update message about portal customization.
Now in the same page, the next step is to set up the Radius authentication and access control.
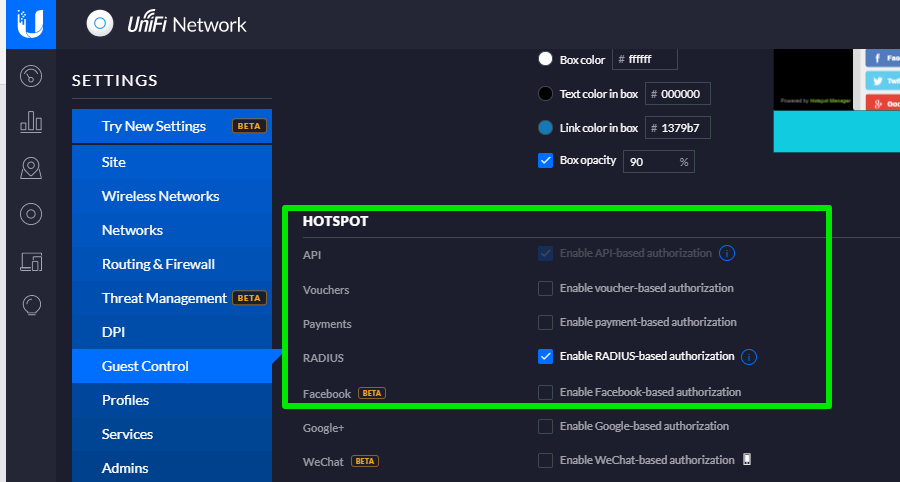
In the Hotspot header, tick Enable RADIUS base authorisation
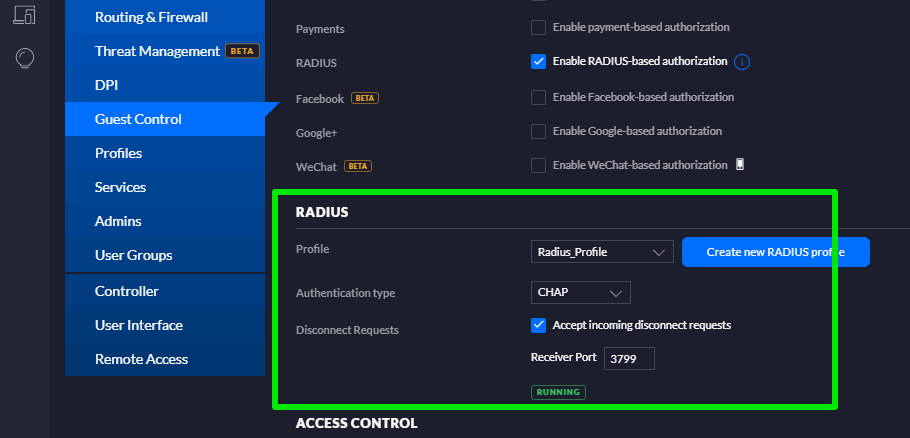
In the Radius header, enter the details as follows:
In the Access Control header, in the Pre-Authorization Access fields configure with:
In the access control section, always enter IPs with CIDR notation even for individual IPs (e.g. 1.1.1.1/32).
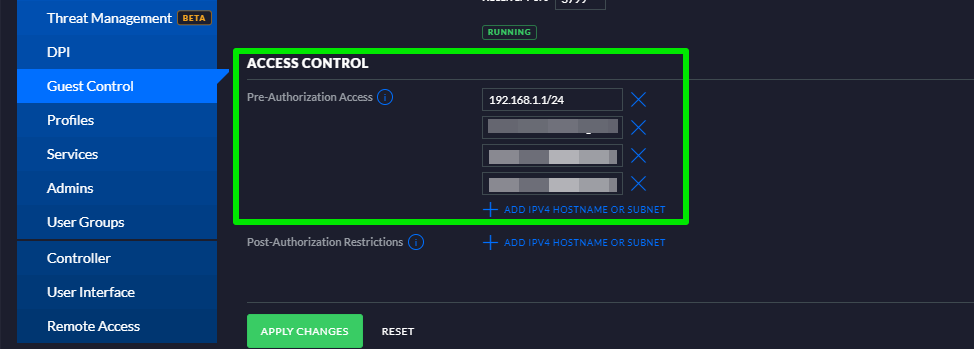
Upon completion of the above steps, click the Apply Changes button to finish.
Now you have the ability to limit the bandwidth assigned to the guests, by creating a User Group.
On the left menu, scroll down to User Group and click Create New User Group.
Configure with Name, Bandwidth Limit (Download), Bandwidth Limit (Upload)
Upon completion of the above steps, click the Save button to finish.
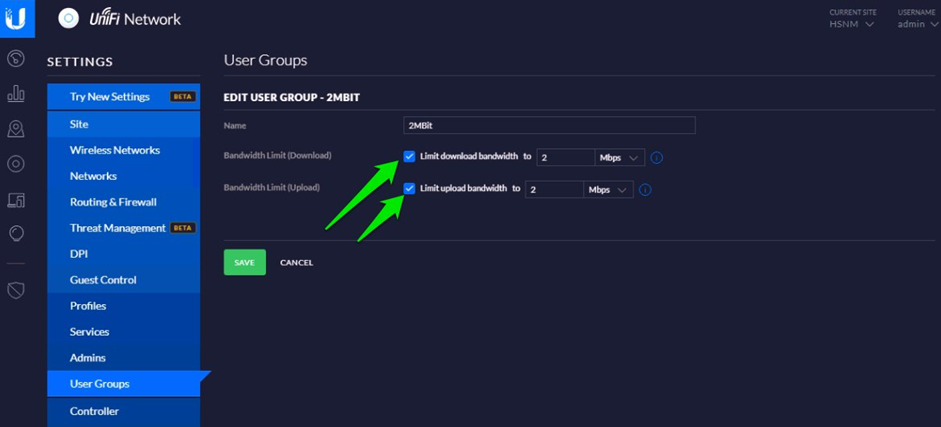
It will take into account the speed you set up here and not the one of the Product Policy in your Wi5stars.
Configure with:
Now you need to apply the User Group to your network. On the left menu, scroll down to Wireless Networks and select your Wireless Network.
Expand the Advanced Options section and select the User Group you have just created.
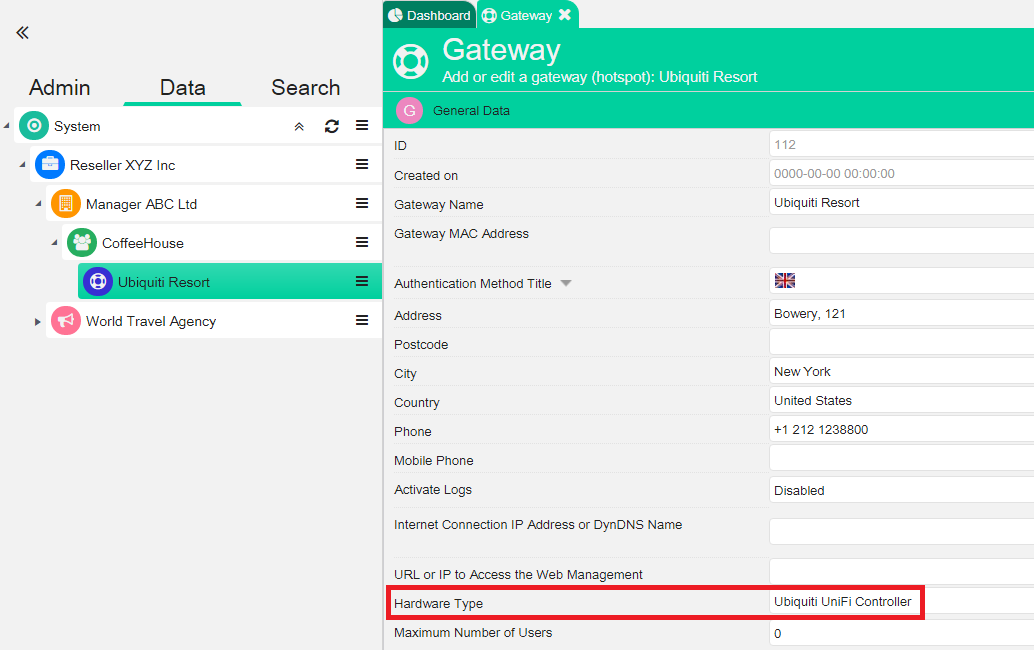
Now access your Wi5stars and select your gateway. In the Hardware Type section, select Ubiquiti UniFi Controller
From the context menu of the gateway, press Download Gateway Config Files to download the configuration zip file.
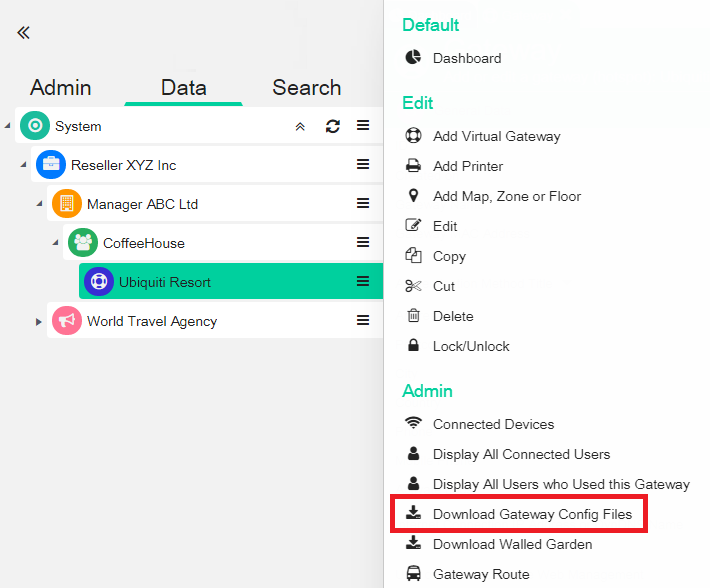
Once the zip file is unpacked, you will find the following files:
The files must be edited in the Ubiquiti Themes folder. The paths vary depending on the SO where the Ubiquiti Controller is installed:
For some Linux distributions, path may differ:
/opt/UniFi/data
/var/opt/UniFi/data
You don’t need to edit the MAC address of the gateway in your Wi5stars.
In your firewall, configure the port forward to accept disconnection requests from your Wi5stars (the same as in the “Radius Authentication and Access Control” paragraph and prerequisites).
You need to create the rule must with the following characteristics:
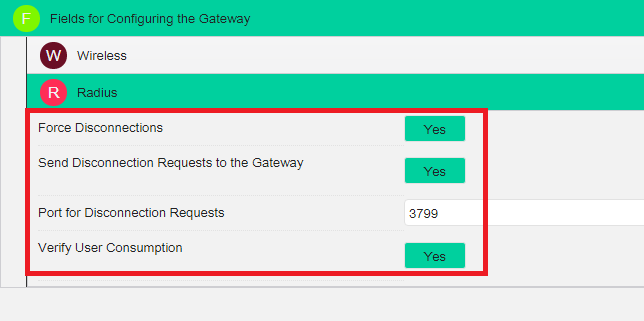
If your Unifi controller is behind a nat or a firewall, you need to enable the port forward of the port previously chosen in the “Radius Authentication and Access Control” paragraph toward the IP of the USG WAN (the same as in the prerequisites).
For Ubiquiti-type gateways, you need to enable these settings for the reasons listed below:
In case you need to configure the access over HTTPS, you need to follow the steps below:
Decide which FQDN to dedicate to the Unifi controller (in our test unifi.wi5stars.com)
Purchase a valid certificate (in our case wildcard certificate .wi5stars.com)
Make sure that you have the complete chain (cert, intermediate, root) of your own certificate because UNIFI controller requires it. If you already have the full chain, then skip to the HTTPS keystore section otherwise continue in this section.
Purchase a valid certificate (in our case wildcard certificate *.Wi5stars.com)
If the full chain is not available, you can use the following online utility: https://tools.keycdn.com/ssl to trace the correct concatenation.
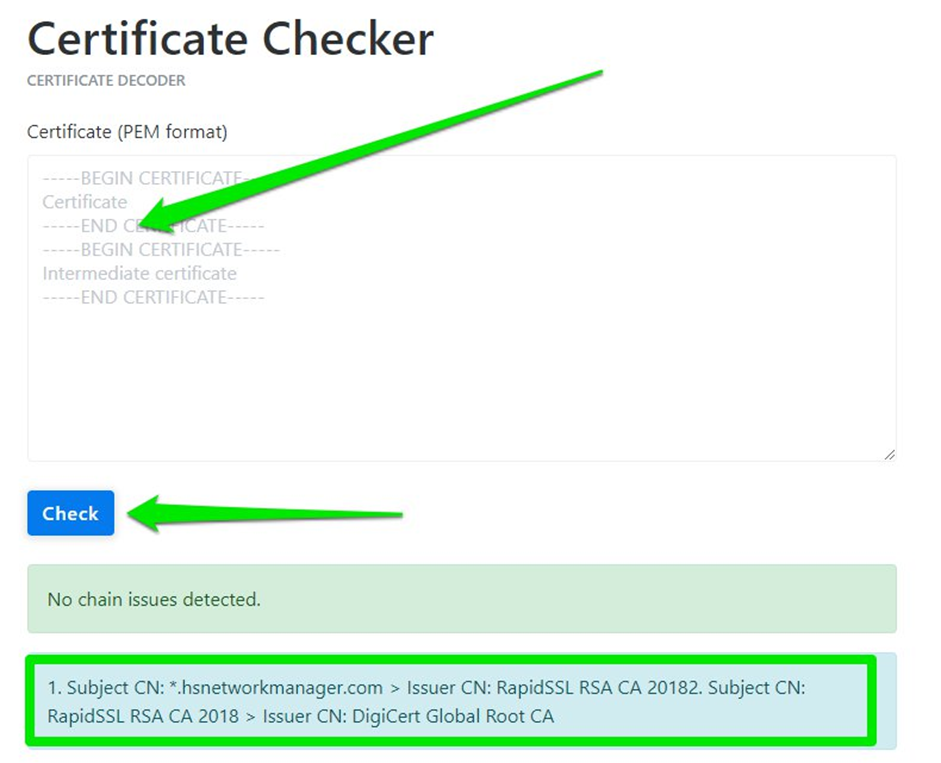
In our test we initially had the CRT and CA-intermediate and not the root. (You can deduct it that in the form we have pasted only 2 —–BEGIN CERTIFICATE—– —–END CERTIFICATE—–).
After a small search we went back to the missing root certificate (in the previous box identified by ISSUER CN):
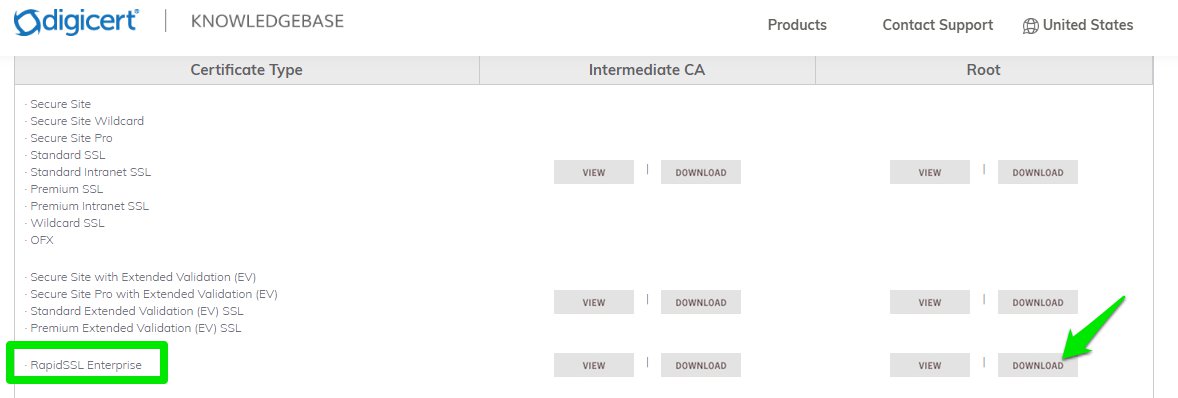
and the root cerfiticate in our case, is available at the issuer’s official website:
https://knowledge.digicert.com/generalinformation/INFO4033.html#links
Beware, this may vary depending on the issuer you choose for the certificate.
Once we have the entire chain available, repeat the verification on the site https://tools.keycdn.com/ssl to make sure that the complete chain is now correct.
(This time the —–BEGIN CERTIFICATE—– —–END CERTIFICATE—– should be 3)
We should be in this final situation:
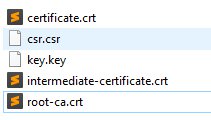
With a text or cli editor, we put certificate-intermediate-root into a single file, in the order in which we tested it in the online tool.
In our case we will name the final file as fullcert.crt
Install the following software https://keystore-explorer.org/downloads.html
Create a new JKS-type keystore
Click on Tools > Import Key Pair
Select the certificate format (in our case we used PKCS #8)
Select the key and the concatenated fullcert you created earlier
Uncheck Encrypted Private Key if you don’t have any type of passphrase set for the certificate, or type the Decryption Password of your certificate
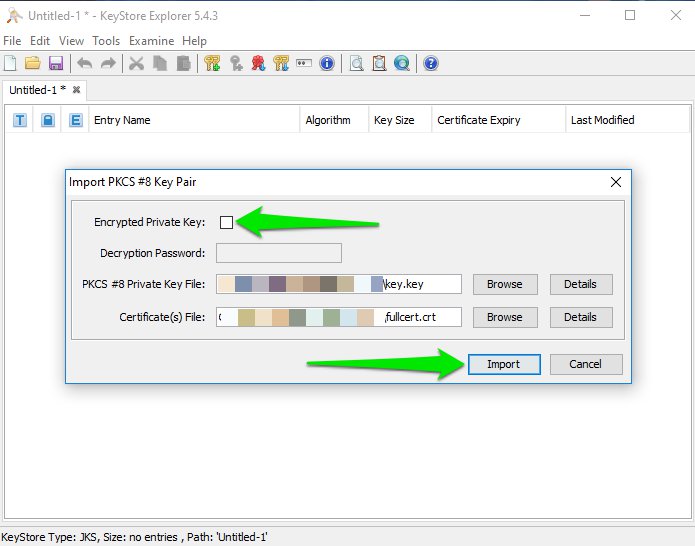
Click Import and choose Unifi as alias
Set as password aircontrolenterprise and as key pair and re-insert it for confirmation
Click on File > Save as
Set the keystore password aircontrolenterprise
Upload the new file created in the Unifi folder by replacing the existing “keystore” file.
The path of the file depends on the SO version where the UniFi controller is installed.
Restart ace.jar or the controller directly in case, for example, it is installed in a WINDOWS environment.
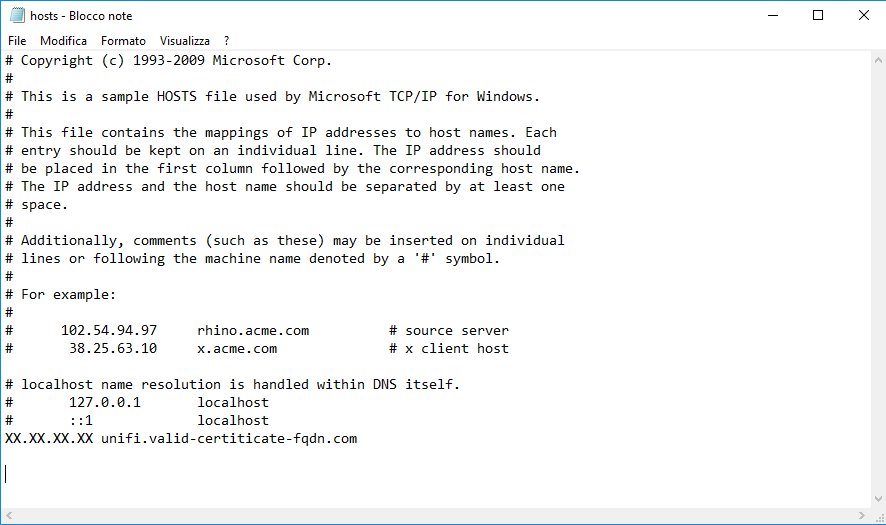
Optional: to verify from the front end of the controller that the installation was successful, change the hosts file to point the public IP with which the USGWAN exits, to a valid FQDN for the certificate:
C:\Windows\system32>notepad c:\Windows\System32\drivers\etc\hosts
Save the change and through CMD, test the real changes of the host file with the command:
Ping execution unifi.valid-certificate-FQDN.com [IPCONFIG] with 32 bytes of data
Reply from IPCONFIG: byte=32 time=1ms TTL=62
Reply from IPCONFIG: byte=32 time<1ms TTL=62
In this section, now you need to configure a port forwarding in your WAN firewall and in the Unifi controller to allow the interface to access from outside.
Go to the Settings menu, then scroll down to Routing & Firewall and select Port Forwarding. Enter the details as follows:
The UC port is the 8443 that, as shown in the below picture, is redirected to the private IP of the Unifi controller with TCP protocol, limited to the connection public IP from which we access.
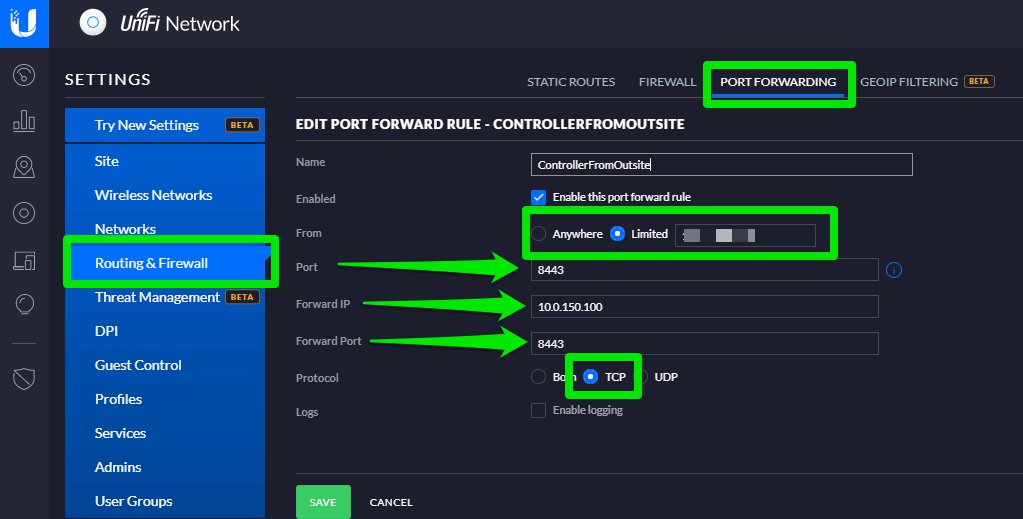
Click Save in the bottom left corner of the page. Your selected entries are saved
At this time, we can invoke via browser the controller from the whitelisted IP. In case the installation of the certificate is successful, you will reach the portal in HTTPS.
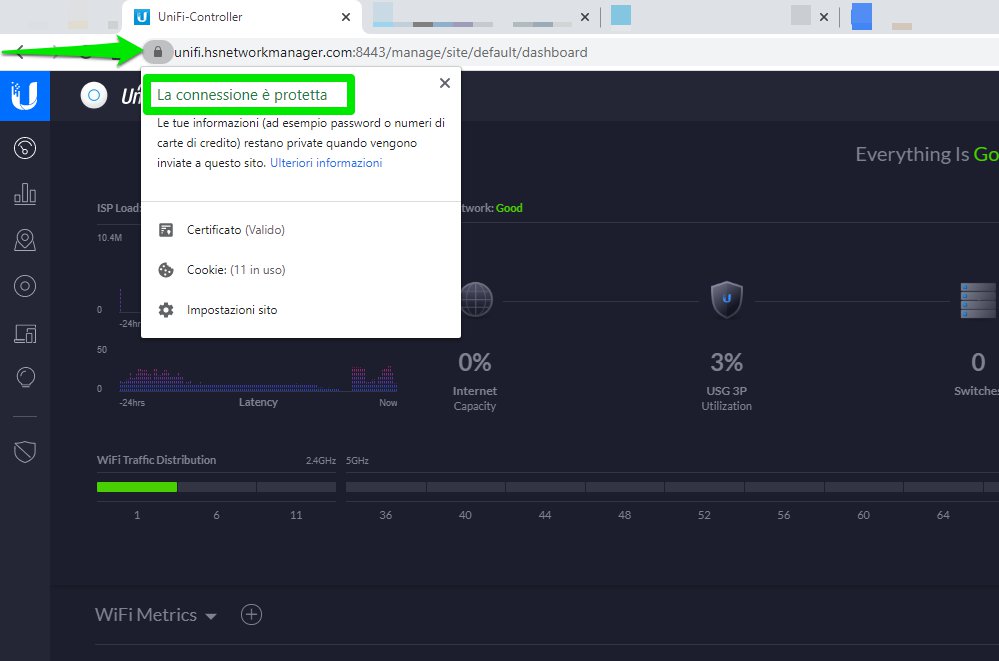
If you do not get this point with the certificate correctly installed, you will need to check all the previous points described in the current “HTTPS Keystore” paragraph and the actual routing of ports in the firewalls. If the installation has been successful, the last “optional” part can be removed.
In this section, you can configure the ability to use the HTTPS protocol.
You need to redirect the 8843 TCP port (default for HTTPS external port) to the controller IP limited to the network class chosen for the private LAN (in our case 10.0.150.1/24).
Go to the Settings menu, then scroll down to Routing & Firewall and select Port Forwarding.
Select the options as follows:
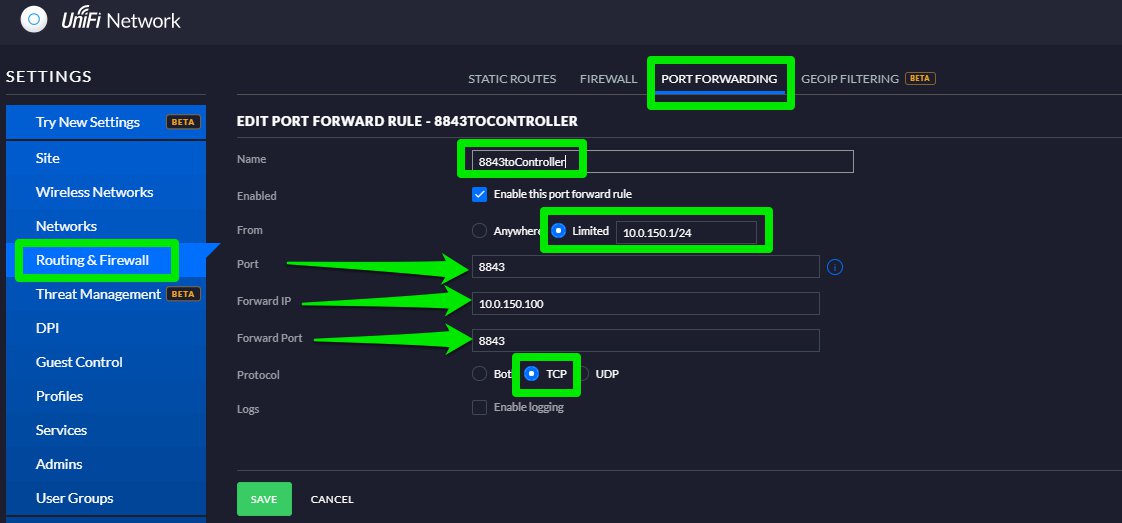
Click Save in the bottom left corner of the page. Your selected entries are saved.
Now you need to configure the Guest Control to use the HTTPS protocol
Go to the Settings menu, then scroll down to Guest Control.
Select the options as follows:
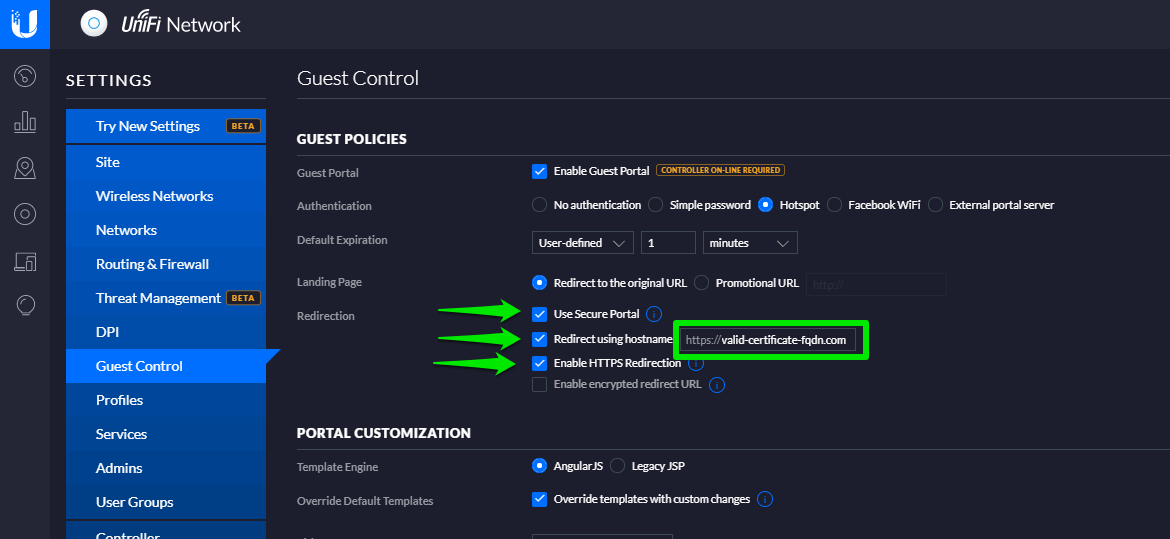
Once completed, click the Save button
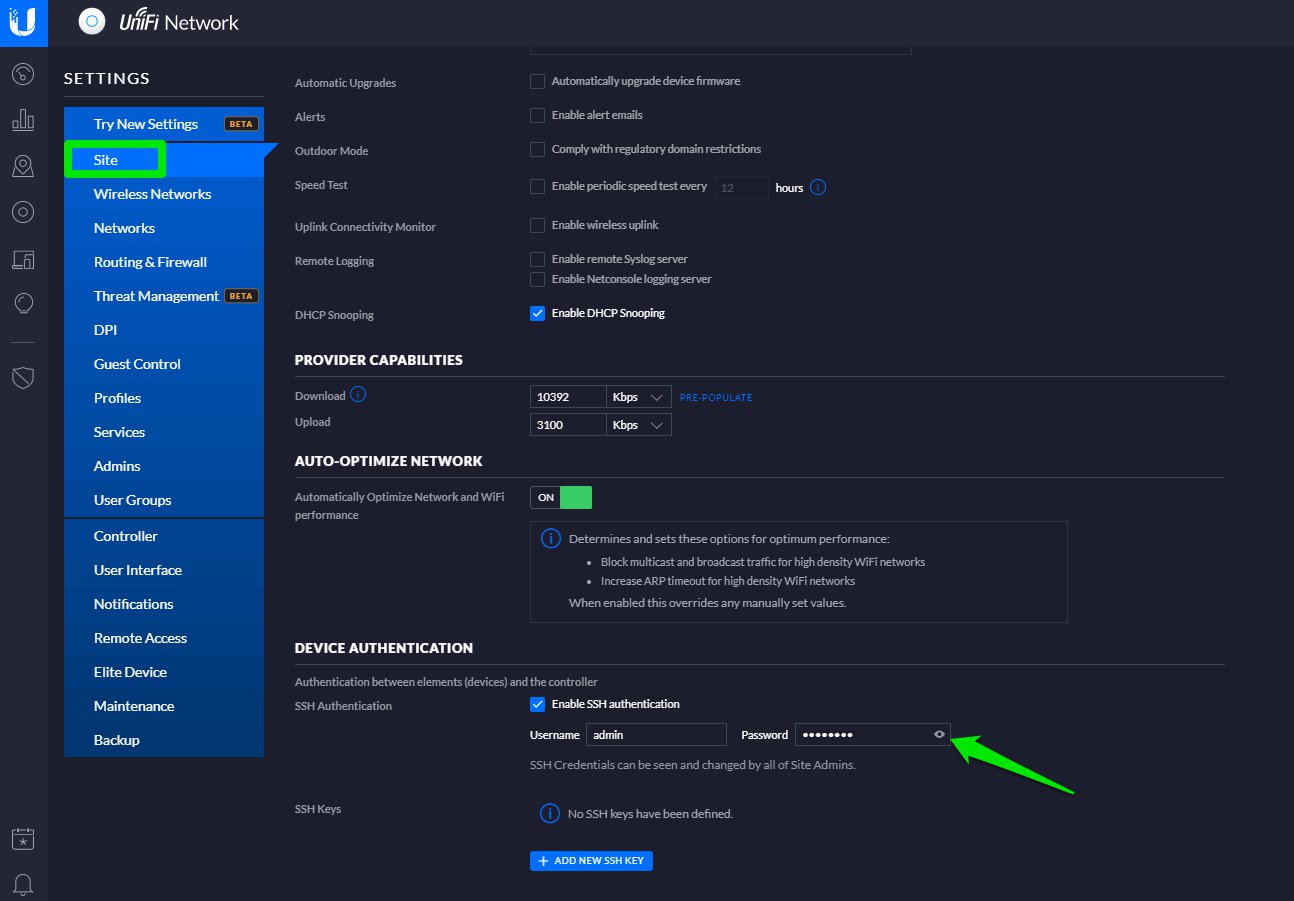
Now you need to recover the SSH access password of the devices.
Go to the Settings menu, then scroll down to Site.
Select the options as follows:
Use a shell to access via SSH to your own USG and enter the following STATIC DNS:
sudo vi /etc/dnsmasq.d/dnsmasq.static.conf
digit
address=/chosenhostname in the previous point/CONTOLLERIPLANPRIVATE
in our case
address=/unifi.valid-certificate-FQDN.com/10.0.150.100
save the new (:wq) file creted and run
sudo /etc/init.d/dnsmasq force-reload
Execute a ping text to unifi valid-certificate-FQDN.com from the USG.
If the solved IP is the one just edited, you have successfully executed the STATIC DNS.
admin@USG:~$ ping unifi. valid-certificate-FQDN.com
PING unifi (10.0.150.100) 56(84) bytes of data.
64 bytes from unifi (10.0.150.100): icmp_req=1 ttl=128 time=1.19 ms
64 bytes from unifi (10.0.150.100): icmp_req=2 ttl=128 time=0.758 ms
This procedure will become permanent even if the USG is re-provisioned.
Go to the Settings menu, then scroll down to Networks
Enter the details as follows:
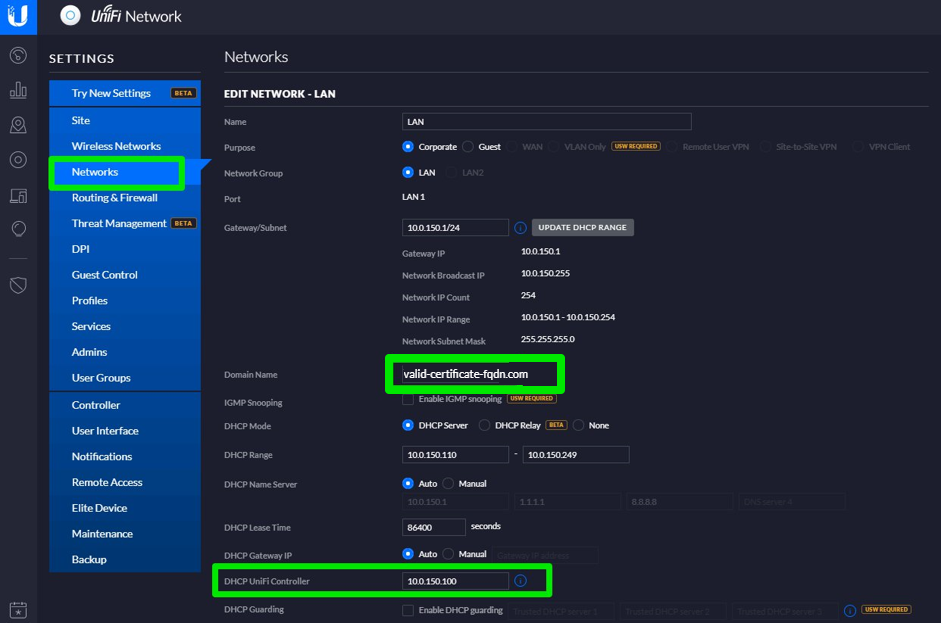
Click the Save button that displays at the bottom left of the window.
You can now redirect to the Welcome Portal with a secure HTTPS protocol.